When the Battlefield Goes Digital: A Boardroom Briefing on Conflict-Era Cyber Risk in the GCC

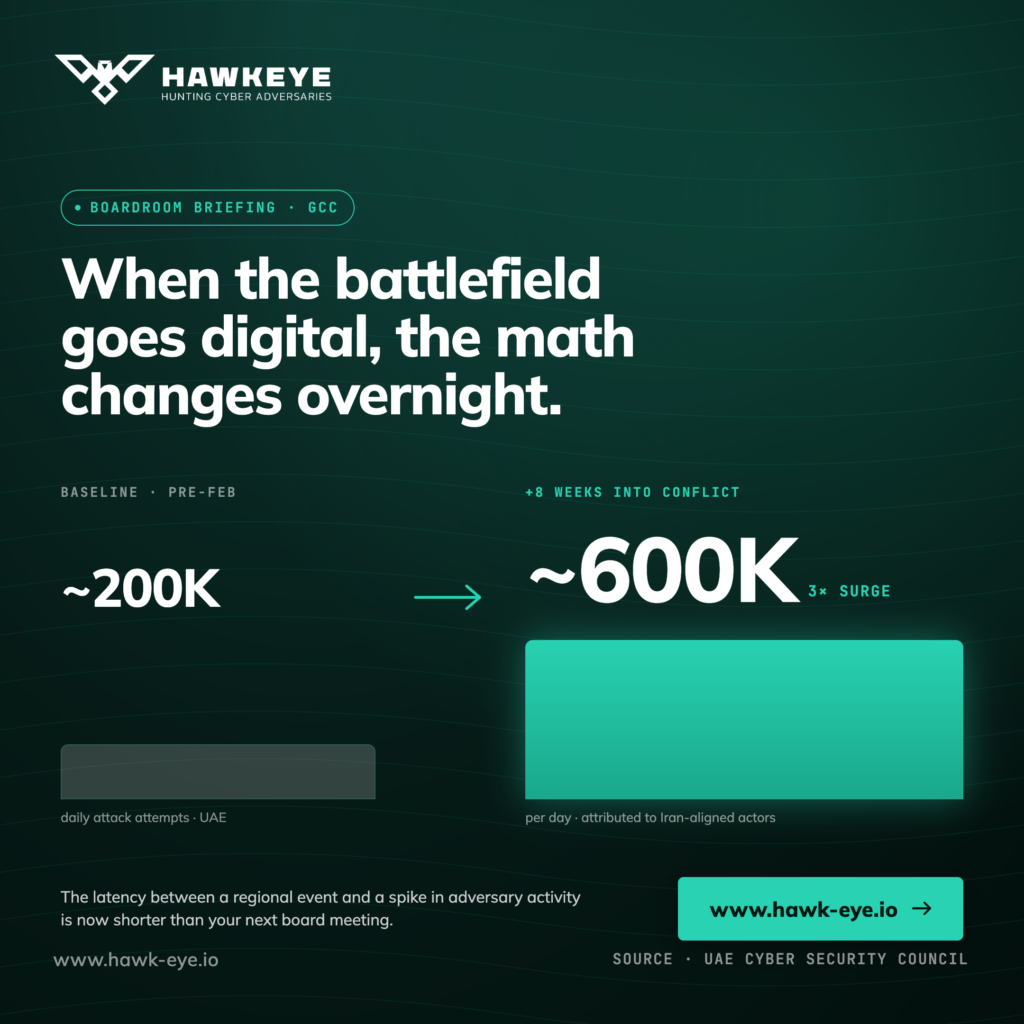
The 600,000 number every GCC board should know
In the eight weeks since regional conflict re-ignited at the end of February, daily cyberattack attempts against the United Arab Emirates have risen from a baseline of around 200,000 to nearly 600,000. That is a threefold surge, and the UAE Cyber Security Council attributes it primarily to Iran-aligned independent actors targeting financial services, government platforms, ports, and utilities. Identity-theft exposure is up 32% year-on-year, and authorities now estimate that one in three individuals in the country may have been brushed by an attempted compromise so far in 2026.
For a CISO, those are operational numbers. For a board, they are a strategic signal. The gap between those two readings is exactly where most enterprises in the region are losing time. This post is written for that gap. It is not a threat-intelligence dump and it is not a product pitch. It is a short briefing on how to translate today’s conflict-era cyber posture into language and cadence a board can act on, in the quarter we are already in.
SIEM: The Data Aggregation Workhorse
Security Information and Event Management (SIEM) has been a fixture in enterprise security programs for over two decades. At its core, a SIEM collects log and event data from across the environment, firewalls, endpoints, servers, applications, identity systems, aggregates it into a central repository, and makes it searchable and correlatable.
The value SIEM delivers is fundamentally about visibility and audit trails. It answers the question: what happened, and when? For organizations with compliance requirements, PCI-DSS, HIPAA, SOC 2, ISO 27001, SIEM is often a non-negotiable baseline. Auditors want log retention, and SIEM delivers it reliably.
The challenge is that collecting data and acting on it are two very different things. A SIEM generates alerts. What it does not do is investigate those alerts, validate them, or contain a threat. That work falls on the analysts sitting behind it. In organizations with a mature, well-staffed Security Operations Centre (SOC), SIEM performs well. In organizations without that capacity, it becomes an expensive alert generator with a backlog no one has time to clear.
The honest limitation: SIEM excels at log management, long-term data retention, and compliance reporting. It requires significant analyst time to turn raw alerts into actionable intelligence. If your team cannot dedicate consistent resources to tuning, triage, and investigation, the tool will underdeliver.
The translation window has closed
For most of the last decade, GCC boards treated geopolitical risk and cyber risk as adjacent disciplines that occasionally rhymed. A flare-up in the region might prompt a tabletop exercise. A ministerial statement might prompt a refreshed risk register. The translation from kinetic to digital was slow enough to feel episodic.
That window has closed. Within weeks of the late-February escalation, attack volumes against UAE assets had already tripled. AWS data-centre damage in the UAE and Bahrain forced a wave of unplanned migrations to alternate regions in India and Europe. Western intelligence partners issued warnings of Iran-aligned activity tracked as CL-STA-1128, also known as Cyber Av3ngers and Storm-0784, disrupting programmable logic controllers across U.S. critical-infrastructure operators that share equipment vendors and design patterns with their GCC counterparts.
The lesson for boards is not that cyber follows conflict. That is well-established. The lesson is that the latency between a regional event and a measurable spike in adversary activity is now short enough that the next board meeting is almost certainly too late. If the geopolitical lens only refreshes once a quarter, the cyber posture it drives will be a quarter behind the threat.
What the data is telling us
Three signals stand out across the past two weeks of reporting, and each one should be read as a board-level input rather than a SOC metric.
The targeting is sectoral, not opportunistic. Financial services, government services, ports and utilities are not a random sample. They are the four pillars a state-aligned adversary would prioritise to maximise economic and reputational disruption while staying below a kinetic threshold. Boards in those sectors should now assume they are inside a named target list, not adjacent to one.
The tradecraft is converged. The UAE Cyber Security Council’s own reporting describes adversaries running technical intrusions, AI-generated phishing, business-email compromise and coordinated financial fraud as a single campaign rather than parallel programmes.1 That convergence has direct implications for how a board should think about accountability. Cyber, fraud, customer protection, and brand are no longer separable risks under a single executive sponsor.
The supply chain is part of the front line. The same fortnight that produced the UAE numbers also produced the Mini Shai-Hulud worm in SAP’s npm packages, the Axios npm compromise attributed by Microsoft to North Korea’s Sapphire Sleet, and a malicious Lightning PyPI release.
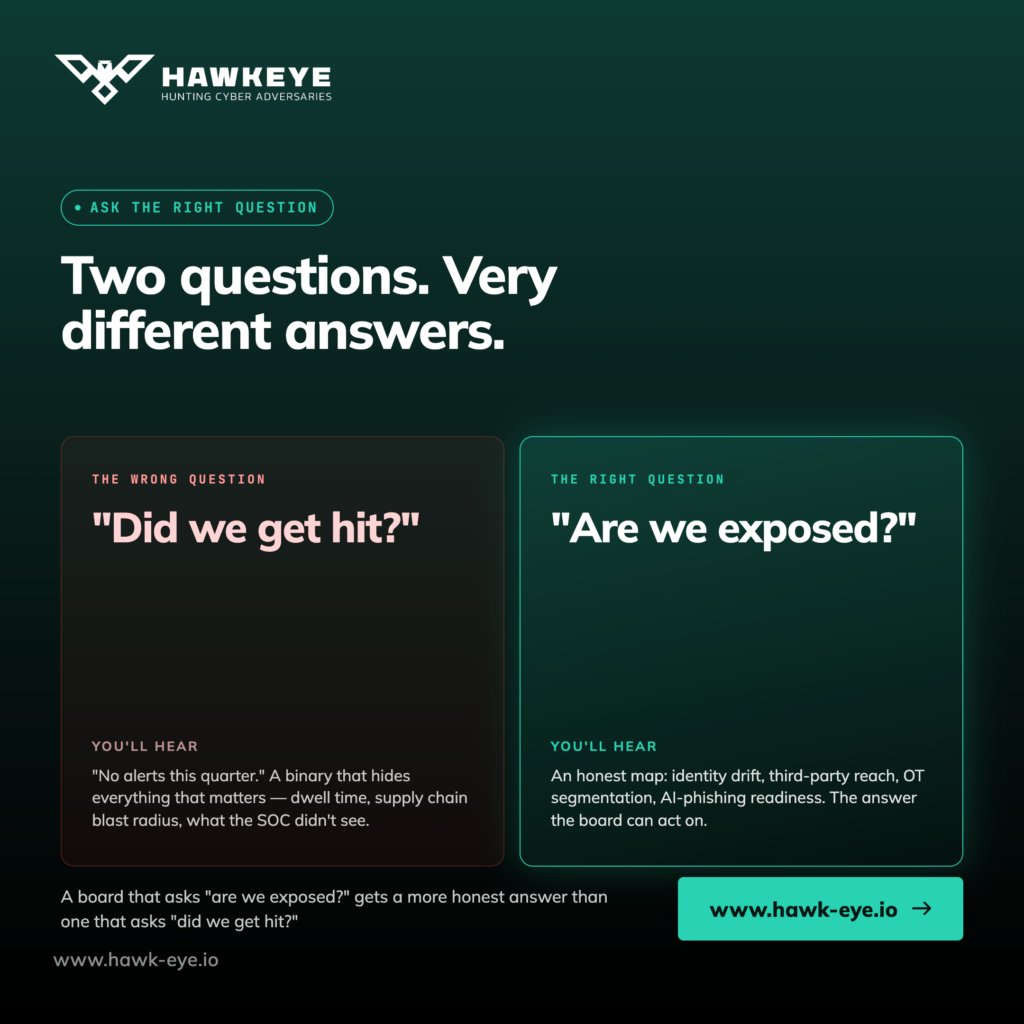
None of those incidents originated in the Gulf, but every Gulf enterprise running modern cloud-native development is downstream of them. A board that asks “are we exposed?” will get a more honest answer than one that asks “did we get hit?”.
Reframing geopolitical risk as a quarterly board input
The remediation here is not a new control. It is a change in the cadence and the framing of the conversation between the CISO and the board. In practical terms, six moves separate organisations that are riding this surge from those that are absorbing it.
The first is to put a standing geopolitical-risk read at the top of every audit-and-risk-committee agenda for the rest of 2026, owned jointly by the CISO and the chief risk officer. The point is not to predict events. It is to ensure the cyber posture has a documented response to events that have already happened.
The second is to commission a fresh threat-led tabletop exercise inside the next 30 days, scoped specifically against the four targeted sectors above and against a conflict-driven escalation scenario. Generic ransomware exercises are no longer sufficient evidence of preparedness.
The third is to pre-authorise a defensive playbook the CISO can execute without further board approval if attempt volumes against the organisation cross a defined threshold. That might mean accelerated patching SLAs in line with CISA’s proposed three-day window for actively exploited flaws, temporary tightening of identity controls, or pre-staged isolation of internet-facing OT assets. Speed is the point.
The fourth is to require quarterly evidence, not assurance, that identity, third-party and OT controls are being tested against current adversary tradecraft, including AI-generated phishing and credential-harvesting supply-chain attacks. Boards should ask to see the artefact, not the summary.
The fifth is to demand a written statement of cloud-residency and resilience posture in light of the regional data-centre disruptions of March. Migration is a board-level decision. It should not be made on a forwarded email at midnight.
The sixth is to revisit cyber-insurance coverage in the same cycle. Carriers globally are conditioning renewal on documented adversarial red-teaming and AI-specific controls, and those riders are arriving in Gulf markets now. A clean renewal in 2026 will require evidence that did not exist in the 2025 file.
None of these moves require new technology. They require a different rhythm.
The takeaway
The cyber posture appropriate to a 200,000-attempts-a-day baseline is not the cyber posture appropriate to 600,000. The arithmetic is obvious. The governance change it demands is less so. The boards that will come through 2026 well are the ones that stop treating geopolitical risk as a contextual footnote in the cyber report and start treating cyber as the live, measurable expression of geopolitical risk on their balance sheet. The two are now the same conversation.
From Hawkeye
Hawkeye will keep tracking the conflict-era threat curve across the GCC and translating what it means for the people who have to brief a board on Monday morning. If this read echoed something your committee has been circling without quite naming, that is the point.