XDR vs. SIEM vs. MDR: Which Security Model Does Your Organization Actually Need?

Security budgets are tighter than ever, and the pressure to choose the “right” tool has never been higher. SIEM, XDR, and MDR keep appearing in vendor pitches, analyst reports, and procurement reviews, often used interchangeably, which is part of the problem. They are not interchangeable. Each one solves a distinct set of problems, operates on a different model, and makes very different demands on your team.
Getting clarity on the differences is less about following vendor marketing and more about being honest about your organization’s maturity, headcount, and actual risk exposure.
SIEM: The Data Aggregation Workhorse
Security Information and Event Management (SIEM) has been a fixture in enterprise security programs for over two decades. At its core, a SIEM collects log and event data from across the environment, firewalls, endpoints, servers, applications, identity systems, aggregates it into a central repository, and makes it searchable and correlatable.
The value SIEM delivers is fundamentally about visibility and audit trails. It answers the question: what happened, and when? For organizations with compliance requirements, PCI-DSS, HIPAA, SOC 2, ISO 27001, SIEM is often a non-negotiable baseline. Auditors want log retention, and SIEM delivers it reliably.
The challenge is that collecting data and acting on it are two very different things. A SIEM generates alerts. What it does not do is investigate those alerts, validate them, or contain a threat. That work falls on the analysts sitting behind it. In organizations with a mature, well-staffed Security Operations Centre (SOC), SIEM performs well. In organizations without that capacity, it becomes an expensive alert generator with a backlog no one has time to clear.
The honest limitation: SIEM excels at log management, long-term data retention, and compliance reporting. It requires significant analyst time to turn raw alerts into actionable intelligence. If your team cannot dedicate consistent resources to tuning, triage, and investigation, the tool will underdeliver.
XDR: Cross-Layer Detection Built for Speed
Extended Detection and Response (XDR) emerged as a response to a specific problem: traditional security tools were generating too much data in isolated silos, and analysts were spending more time switching between consoles than actually investigating threats.
XDR breaks those silos. It integrates data from endpoints, network traffic, cloud workloads, identity systems, and email into a single detection and response platform. Rather than presenting raw logs, XDR correlates signals across these layers to surface coherent threat stories, linking an anomalous login to a lateral movement event to a suspicious file execution, for example.
This cross-layer correlation is XDR’s primary advantage. An attacker who moves from a phishing email to a compromised endpoint to a cloud storage exfiltration leaves traces in multiple systems. SIEM can collect all of those traces; XDR is built to connect them automatically and surface the full attack chain as a single, prioritized incident.
Automation sits at the center of the XDR model. Containment actions, isolating an endpoint, blocking a user account, revoking a session, can be triggered automatically or with a single analyst click, dramatically compressing response time. Solutions like Hawkeye’s CSOC and XDR platform (https://hawk-eye.io/hawkeye-csoc-and-xdr/) are built around this principle: reducing the gap between detection and containment through unified telemetry and automated playbooks.
XDR does not collect more data; it makes better use of the data that already exists across your security stack.
The tradeoff is that XDR still requires in-house expertise to run effectively. Someone needs to manage the platform, refine detection logic, handle escalations, and translate alerts into business decisions. For organizations that have security engineers but lack the tooling to connect their stack, XDR is an excellent fit. For organizations that lack the people to run it, the technology alone will not close the gap.
MDR: The Fully Managed Option
Managed Detection and Response (MDR) is a service, not a product. This is the distinction that trips people up most often.
An MDR provider brings its own technology stack, often including XDR or SIEM capabilities and, critically, its own team of analysts, threat hunters, and incident responders. The organization does not need to staff a SOC; the MDR provider operates as one on its behalf, monitoring the environment around the clock and taking response actions when threats are confirmed.
MDR is built for organizations that need strong security outcomes but cannot or should not build the internal capability to achieve them. This covers a wide range: mid-market companies without a dedicated security team, enterprises that want to extend their coverage to 24/7 without tripling headcount, and any organization that has concluded that outsourcing detection and response is more cost-effective than building it from scratch.
What makes a good MDR engagement is the quality of human judgment behind it. Automated detection gets you part of the way; experienced analysts who understand attacker behavior, your specific environment, and when to escalate versus contain are what make MDR worth the investment. Hawkeye’s AI-driven capabilities (https://hawk-eye.io/hawkeye-ai/) reflect where the market is heading, augmenting human analysts with machine speed and pattern recognition, so that the humans can focus on decisions that require context rather than raw throughput.
The honest limitation: MDR means accepting a degree of dependency on an external provider. Response actions, escalation paths, and communication protocols need to be clearly defined upfront. Organizations with complex regulatory requirements around data sovereignty also need to scrutinize how their MDR provider handles data before committing.
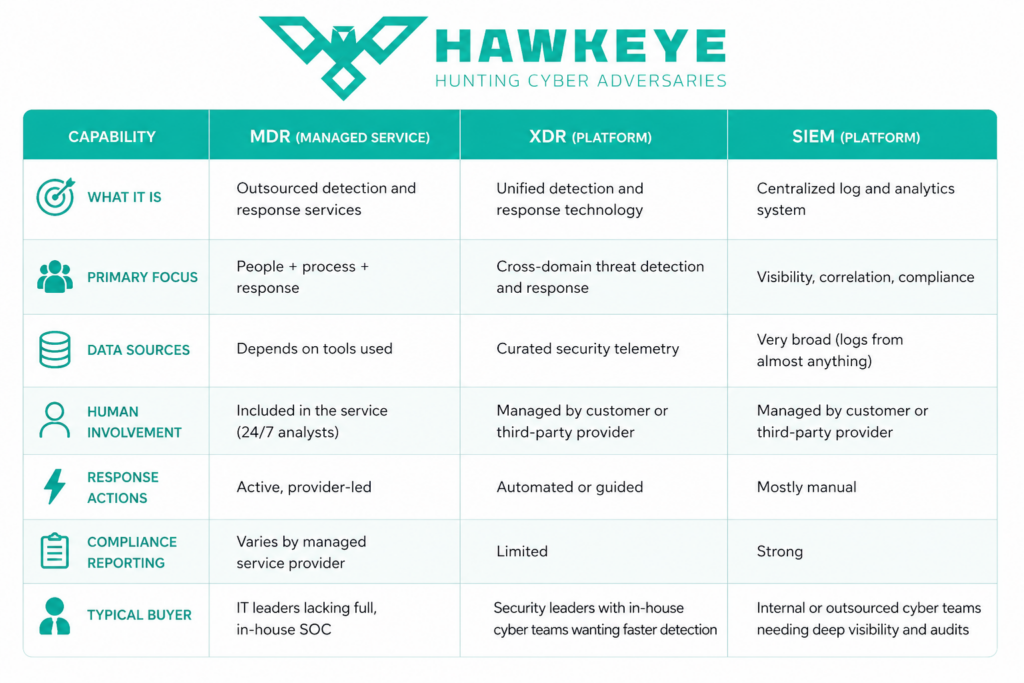
MDR vs XDR vs SIEM Comparison Table
MDR, XDR, and SIEM address different layers of modern security operations, with some overlap between MDR and XDR. SIEM and XDR are technologies, while MDR is a service model. SIEM serves as the source of truth for cybersecurity data. MDR and XDR cover monitoring and threat detection, with MDR providing technology and service, while XDR offers technology without the service layer.
Here’s how the three solutions compare in detail.
Making The Decision
The most common mistake organizations make is treating this as a technology decision rather than an operational one. The right question is not “which tool is more advanced?” It is “which model fits how our security team actually operates?”
If compliance is the primary driver, SIEM belongs in your stack. Log retention, audit trails, and regulatory reporting are its native language. Pair it with sufficient analyst capacity and clear alert triage processes, and it will serve its purpose.
If you have a security team but fragmented tooling, XDR addresses the exact problem of too many consoles generating too many siloed alerts. It consolidates detection across layers, accelerates investigations through automated correlation, and reduces the cognitive load on analysts stitching together an attack narrative from disparate data sources.
If you cannot staff a security function internally, MDR is the pragmatic path. You get continuous monitoring, expert analysis, and active response without having to build the infrastructure yourself. The key is vetting providers on the depth of their human expertise, not just their technology capabilities.
If you need coverage across all three dimensions, many mature organizations run a combination: SIEM for compliance and long-term log management, XDR for cross-layer detection and automated response, and MDR to extend 24/7 human coverage beyond what their internal team can provide. This layered approach is increasingly common and reflects a realistic view of where each model adds distinct value.
Security decisions made on marketing language tend to underperform. Security decisions made against an honest assessment of your environment, your team’s capacity, and your actual risk exposure tend to hold up. Start there, and the choice between SIEM, XDR, and MDR becomes considerably more straightforward.