AI-Powered SOC: How Agentic Security Operations Are Augmenting the Traditional Model

AI-powered SOCs are transforming how security teams detect, triage, and contain threats in 2025. Learn how agentic AI, automated response, and human-led oversight are redefining modern cybersecurity operations.
The Breaking Point of the Traditional Security Operations Center
Security Operations Centers were not built to fail. They were built for a threat landscape that no longer exists. When the tiered analyst model was designed, alert volumes were manageable, threats moved slowly, and a capable Tier 1 team could meaningfully clear a queue before the next shift. That world is gone.
Studies indicate that SOC teams now receive an average of 4,000 or more alerts daily, the vast majority of which are false positives or low-priority notifications. HawkEye The result is a “needle in a haystack” problem that no number of human analysts can solve at current scale. Critical threats go uninvestigated not because of negligence, but because there are simply not enough hours or hands. Analyst burnout has become a quantifiable operational risk, and suppressing detection rules has become a coping mechanism rather than a strategy.
This is the problem that AI-powered security operations are built to solve. And in 2026, that solution has moved well beyond pilot programmes and vendor promises into production deployment across organisations of every size.
What Makes a SOC "AI-Powered" in 2026
The term “AI SOC” gets used loosely. It is worth being precise about what distinguishes a genuinely AI-powered security operations center from a traditional SOC with a few automation rules bolted on.
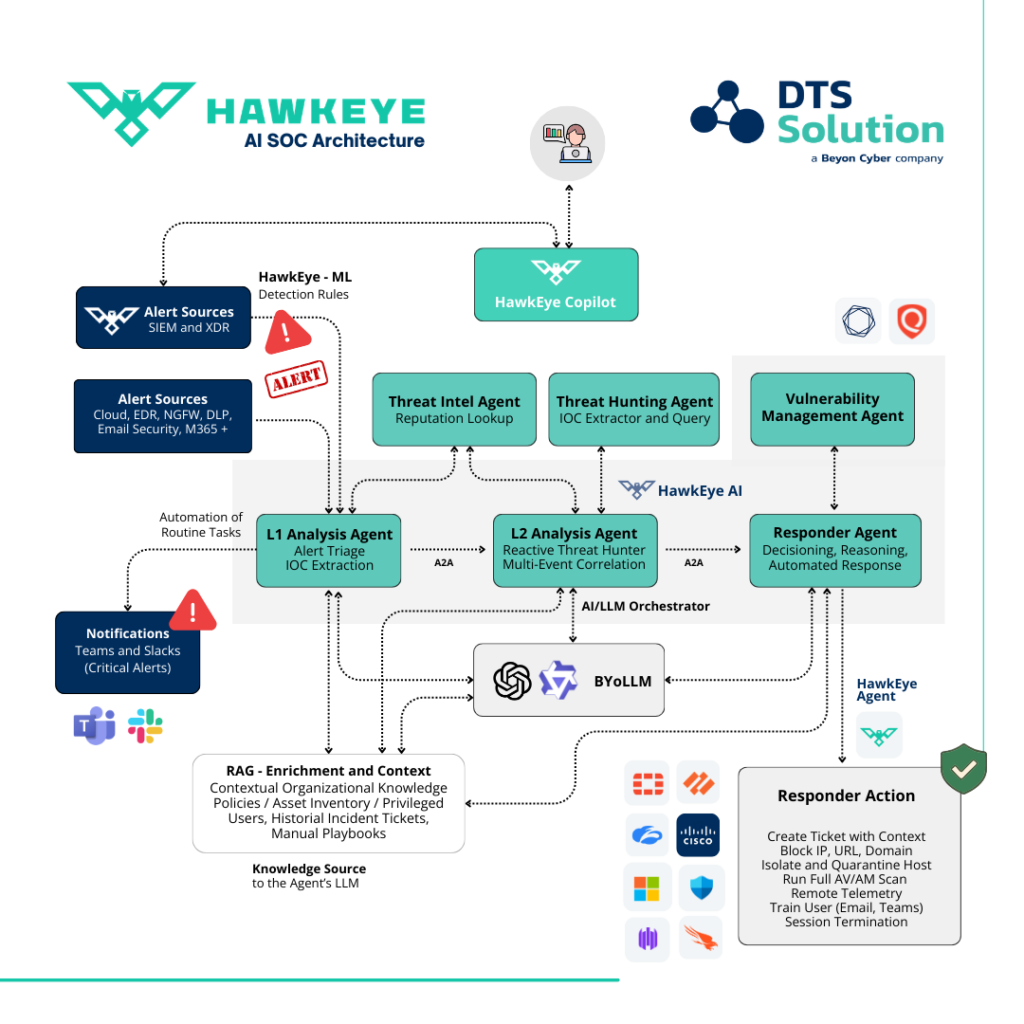
An AI SOC is a security operations center where artificial intelligence handles the bulk of repetitive detection, triage, investigation, and response tasks, enabling human analysts to focus on complex threat analysis, proactive threat hunting, and strategic security decisions. Unlike a traditional SOC that depends on analysts manually pivoting between tools to investigate every alert, an AI SOC uses agentic AI to autonomously collect artifacts, enrich alerts, correlate data, and execute containment actions.
The critical distinction is the word “agentic.” Agentic AI systems do not simply follow pre-written rules or static playbooks. They reason through context, make decisions under uncertainty, chain together investigative steps, and adapt when circumstances deviate from what was anticipated. The AI operates under defined confidence thresholds: high-confidence decisions proceed automatically, while low-confidence or novel situations route to an analyst for review.
This is the architecture that separates modern AI security operations from the legacy SOAR tools that promised automation and delivered brittle, rule-dependent workflows.
The Four Capabilities That Define AI-Driven Threat Detection and Response
- AI-Driven Signal Correlation and Noise Reduction
Generative AI helps analysts triage alerts by correlating threat intelligence and surfacing related activity that might not trigger a traditional alert. It generates rapid incident summaries so teams can get started faster, guides investigations with step-by-step context and evidence, and automates routine response tasks like containment and remediation through AI-powered playbooks.
The practical result is a dramatic reduction in alert volume without sacrificing coverage. Security teams that have deployed AI-driven triage are reporting noise reductions of 50 to 90 percent, with the most advanced platforms achieving the processing of thousands of alerts in the time it previously took an analyst to work through dozens.
- Autonomous Triage and Incident Prioritisation
Traditional SOAR platforms fail the moment an incident deviates from the pre-written logic. Agentic AI systems assess risk dynamically, evaluate context, and prioritise based on actual threat severity rather than rule-based categorisation. The result is that analysts engage only with actionable intelligence, and they do so with richer context already assembled around each incident.
- Automated Containment: Isolate Host, Revoke Identity, Block Traffic
ReliaQuest’s 2026 Annual Threat Report found that attackers achieved lateral movement in just 4 minutes during the fastest incidents in 2025, an 85% acceleration from the prior year, with average breakout times dropping to 34 minutes. A SOC running manual triage processes measured in hours cannot contain threats within that window. Automated containment actions that isolate a compromised host, revoke an identity, or block anomalous traffic within seconds rather than minutes can fundamentally change the blast radius of an incident.
- Agentic Response Playbooks That Adapt to Context
Unlike static automation, AI-driven response playbooks adapt in real time. They incorporate threat intelligence feeds, adjust based on environmental factors, chain investigative steps together, and escalate to human analysts when situations exceed their defined parameters. This is the difference between executing a script and exercising judgment.
The Speed Advantage: Why MTTD and MTTC Are the Metrics That Matter
Mean Time to Detect (MTTD) and Mean Time to Contain (MTTC) are the metrics that most accurately reflect the operational impact of AI in security operations. Organisations using Microsoft Security Copilot report a 30% reduction in Mean Time to Resolution. Platforms built specifically around agentic AI are reporting even larger improvements, with some processing security alerts 20 times faster than traditional methods with measurably higher accuracy.
The business case is not primarily about cost reduction, though that follows. It is about the fundamental ability to operate at the tempo that modern threats require. According to Omdia’s 2025 cybersecurity decision maker survey, autonomous SOC evolution may reach full potential and become standard for CISOs within one to two years.
The AI-SOC Organisation Chart: A Three-Layer Model That Works
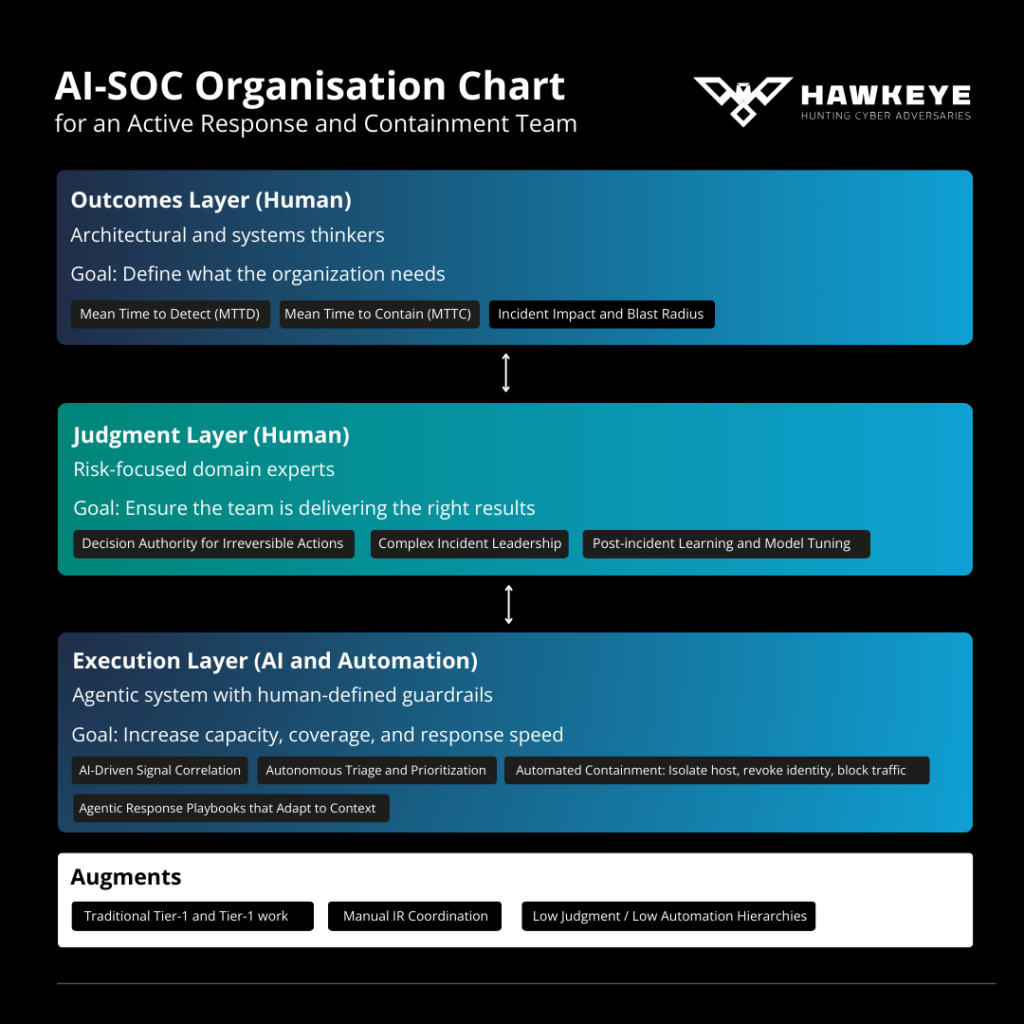
The most important operational insight from AI-SOC deployments is that full automation and full human control are both the wrong answer. What works is a structured layering of human and AI responsibilities, each operating within the domain where it is genuinely superior.
At DTS Solution, our AI-SOC Organisation Chart for Active Response and Containment Teams reflects exactly this architecture.
Outcomes Layer (Human): Architectural and systems thinkers who define what the organisation needs. Their responsibility is setting the metrics that matter: MTTD, MTTC, and Incident Impact and Blast Radius. These are business outcomes, not technical outputs.
Judgment Layer (Human): Risk-focused domain experts who ensure the team is delivering the right results. Decision authority for irreversible actions, complex incident leadership, and post-incident learning all live here. Human judgment governs the decisions that carry real-world consequences.
Execution Layer (AI and Automation): The agentic engine of the modern SOC, operating within human-defined guardrails to increase capacity, coverage, and response speed. AI-driven signal correlation, autonomous triage, and automated containment execute here at machine speed.
This architecture replaces the low-value work of traditional Tier 1 and Tier 2 operations, manual IR coordination, and the low-judgment, low-automation hierarchies of legacy SOC models. It does not replace human expertise. It elevates it to where it actually matters.
HawkEye AI: Precision Threat Detection Built for This Architecture
DTS Solution’s HawkEye AI platform was designed from the ground up around the principles that define effective AI-powered security operations. Its mission is to drastically reduce response times, improve threat prediction accuracy, and minimise false positives, enabling organisations to stay ahead of cyber risks with greater precision and efficiency.
HawkEye AI applies machine learning and AI across five critical domains:
Pattern Matching for Advanced Threat Detection: HawkEye AI uses pattern-matching ML algorithms to identify deviations from established behavioural norms. This includes detecting domain generation algorithm (DGA) patterns in DNS traffic commonly associated with malware communication, identifying unusual login activities that could indicate brute-force attacks, and flagging lateral movement through abnormal traffic patterns. The platform continuously learns from new threat data, adapting to evolving attack techniques and improving detection of zero-day attacks and insider threats while reducing false positives.
Entity Behaviour Analysis: AI-powered entity behaviour analysis monitors and analyses typical behaviour patterns of users, devices, processes, and systems. When deviations from normal behaviour are detected, such as unusual login locations or activity patterns, HawkEye AI flags these anomalies for investigation, enabling identification of insider threats, compromised accounts, and advanced persistent threats with greater accuracy and speed.
Anomaly and Outlier Detection: HawkEye AI identifies deviations from established behaviour baselines in network traffic, user activities, and system performance. This approach is particularly effective at detecting unknown and unseen attacks by flagging outliers in real time, enabling proactive response to emerging threats that traditional signature-based detection methods would miss.
Generative AI in Cyber Threat Intelligence: HawkEye AI uses generative AI to process cyber threat intelligence from threat feeds, vulnerability databases, security advisories, OSINT, and other sources. The AI analyses this data to determine its relevance to deployed technologies, industries, and specific regions, then enriches it by categorising threats, assessing severity, and assigning urgency. This automated process ensures that the most critical and relevant threats are prioritised, providing tailored and actionable insights.
The platform targets a 90% reduction in false positives, an 85% reduction in MTTR, an 80% improvement in SOC analyst efficiency, and a 92% enhancement in prediction accuracy. These are not marketing figures. They are operational targets that drive every design decision in the platform.
The Threat Landscape Is Driving Urgency
The case for AI-powered SOC transformation is not only defensive. Adversaries are deploying agentic AI capabilities too. AI-driven phishing attacks increased 703% in 2024 to 2025. Agentic ransomware can now automate the full chain of compromise, from reconnaissance to exfiltration, in minutes rather than the days or weeks traditional operations required. Nation-state actors have been documented using AI to run the majority of a complex attack chain autonomously, with human operators providing only high-level direction.
Speed is one of the biggest improvements AI brings. Today’s threats evolve quickly, and delays in detection give attackers the upper hand. AI helps SOCs spot risky behaviour within seconds rather than hours. A SOC operating at human speed will be outpaced by adversaries operating at machine speed. The defensive response must match the tempo of the threat.
Conclusion: The AI-Powered SOC Is Not Optional
The question is no longer whether to adopt AI in security operations. For organisations serious about resilience, that decision has been made by the threat landscape. The question is how to do it well, with the right architecture, the right governance, and the right balance between machine capability and human judgment.
The AI-powered SOC is transforming how companies defend against digital threats. With faster detection, fewer false alarms, and smarter workflows, security teams are better equipped to protect what matters.
At DTS Solution, we have been building and operating Managed CSOC and XDR services across the UAE, GCC, and EMEA for over a decade. HawkEye AI delivers the execution-layer capabilities that the modern AI-SOC demands, within a three-layer architecture that keeps human judgment where it belongs: governing outcomes, leading complex incidents, and making the decisions that matter most.
To explore how DTS Solution and HawkEye can help your organisation build an AI-ready Security Operations Center, contact us at [email protected] or visit www.hawk-eye.io.