Harvesting Browser Credentials: The DPAPI Exploitation Threat

Credential harvesting techniques have shifted dramatically as security controls improve around traditional attack vectors. While organizations invest heavily in protecting LSASS processes and memory-based credential extraction, attackers have adapted their methods to target stored browser credentials. This technique presents significant risk as browsers increasingly serve as credential repositories for users across enterprise environments.
The shift toward browser credential harvesting reflects the security principle that attackers will always find the path of least resistance. As endpoint detection and response solutions improve their LSASS monitoring capabilities, threat actors have redirected their efforts toward browser-stored credentials, which often receive less defensive attention despite containing the same sensitive authentication data.
The Mechanics of Browser Credential Storage
Modern browsers implement sophisticated encryption mechanisms to protect stored credentials. Google Chrome, Microsoft Edge, and other Chromium-based browsers utilize Windows Data Protection API (DPAPI) to encrypt login data before storage. This encryption occurs through the CryptProtectData function, which creates user-specific encrypted blobs that theoretically can only be decrypted by the same user on the same system.
The Windows Data Protection API (DPAPI) forms the foundation of browser credential security on Windows systems. This Microsoft-developed framework provides cryptographic protection for sensitive data by binding encrypted content to specific user accounts and machine contexts. The encryption process occurs transparently when users choose to save credentials in their browsers.
DPAPI operates through two primary functions: CryptProtectData for encryption and CryptUnprotectData for decryption. The encryption key derives from the user’s login credentials, creating a theoretically secure system where only the original user can decrypt their stored data on the same machine where it was encrypted.
The DPAPI implementation relies on the following Windows API structure:
DPAPI_IMP BOOL CryptProtectData(
[in] DATA_BLOB *pDataIn,
[in, optional] LPCWSTR szDataDescr,
[in, optional] DATA_BLOB *pOptionalEntropy,
[in] PVOID pvReserved,
[in, optional] CRYPTPROTECT_PROMPTSTRUCT *pPromptStruct,
[in] DWORD dwFlags,
[out] DATA_BLOB *pDataOut);
Browsers store this encrypted data in specific file locations within the user’s AppData directory. Google Chrome maintains credentials in Login Data files, while encryption keys reside in Local State files. Microsoft Edge follows similar patterns with identical file structures.
Attack Methodology and File Locations
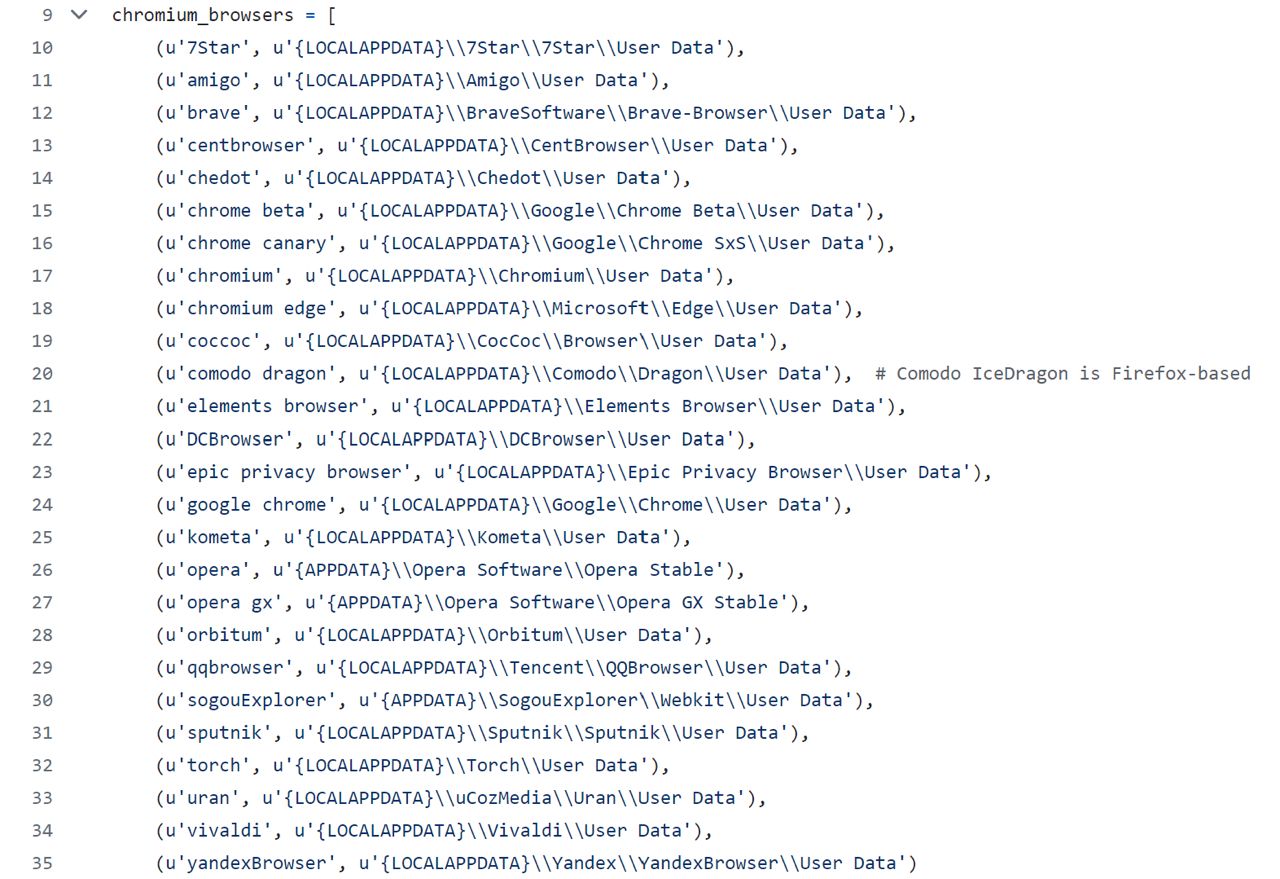
Attackers target specific file paths where browsers store sensitive information:
Google Chrome:
- C:\Users\<username>\AppData\Local\Google\Chrome\User Data\Local State
- C:\Users\<username>\AppData\Local\Google\Chrome\User Data\Default\Login Data
- C:\Users\<username>\AppData\Local\Google\Chrome\User Data\Default\Network\Cookies
Microsoft Edge:
- C:\Users\<username>\AppData\Local\Microsoft\Edge\User Data\Local State
- C:\Users\<username>\AppData\Local\Microsoft\Edge\User Data\Default\Login Data
- C:\Users\<username>\AppData\Local\Microsoft\Edge\User Data\Default\Network\Cookies
The attack process involves retrieving the AES encryption key from the Local State file, then utilizing the CryptUnprotectData API to decrypt credentials stored in Login Data files. This technique maps to MITRE ATT&CK framework technique T1555.003.
Tools and Techniques in Practice
Several tools facilitate browser credential extraction. LaZagne, SharpChrome, DonPAPI, and dploot represent commonly used utilities that automate the credential harvesting process. These tools share common behavioral patterns:
- Access browser-specific file locations
- Extract encryption keys from Local State files
- Call CryptUnprotectData API for decryption
- Parse Login Data databases for credential pairs
SharpChrome execution demonstrates typical attack patterns. The tool operates in memory, extracts AES keys, and performs decryption operations against stored credentials. Remote execution through frameworks like DonPAPI enables credential harvesting across multiple systems using administrative privileges.
Detection Strategies
Effective detection requires monitoring multiple data sources across different system layers. The primary detection opportunities include:
Process Monitoring
Monitor for non-browser processes accessing browser-specific file locations. Process creation events (Event ID 4688) with command-line auditing enabled capture suspicious tool execution patterns. Focus detection on processes accessing Login Data files that originate from non-browser executables.
File System Access
Implement file system auditing on sensitive browser locations. Event ID 4663 captures file access attempts against Login Data files. Configure auditing policies under: Computer Configuration > Windows Settings > Security Settings > Advanced Audit Policy Configuration > Object Access > Audit File System
API Monitoring
The CryptUnprotectData API serves as a critical detection point. Endpoint Detection and Response (EDR) solutions should hook this API to identify unauthorized decryption attempts. Monitor for processes making DPAPI calls that lack legitimate browser context.
Windows Event Analysis
DPAPI-specific events provide detailed decryption telemetry:
- Event ID 4693: Captures DPAPI master key access attempts
- Event ID 16385: Records detailed DPAPI operations including process IDs and operation types
Event ID 16385 contains crucial fields for detection:
- OperationType: Identifies SPCryptUnprotect operations
- DataDescription: Distinguishes browser data from other DPAPI operations
- CallerProcessID: Links decryption attempts to specific processes
Correlation between Event ID 4688 (process creation) and Event ID 16385 (DPAPI operations) using process IDs reveals anomalous activity patterns.
Advanced Detection Techniques
Domain DPAPI Backup Key Monitoring
Attackers with domain administrator privileges may access domain DPAPI backup keys to decrypt any domain user’s stored credentials. Monitor Event ID 4662 for unauthorized backup key access attempts through: Computer Configuration > Windows Settings > Security Settings > Advanced Audit Policy Configuration > Object Access > Audit Other Object Access Events
Behavioral Analysis
Implement detection logic that correlates multiple indicators:
- Non-browser process execution
- Access to browser credential files
- DPAPI decryption operations
- Unusual process relationships
Volume Considerations
DPAPI events generate significant log volume in production environments. Implement filtering strategies focusing on:
- Processes not matching known browser executables
- Multiple credential file access attempts
- Unusual timing patterns in DPAPI operations
Mitigation Approaches
Organizations should implement layered defenses against browser credential harvesting:
Administrative Controls:
- Disable browser password storage through group policy
- Implement privileged access management solutions
- Restrict local administrator privileges
Technical Controls:
- Deploy EDR solutions with API monitoring capabilities
- Enable comprehensive Windows event auditing
- Implement file integrity monitoring on browser directories
Detection Engineering:
- Develop correlation rules linking process creation with file access events
- Create behavioral analytics for DPAPI usage patterns
- Establish baseline metrics for legitimate browser DPAPI operations
Conclusion
Browser credential harvesting represents a significant threat vector as organizations improve protection around traditional credential theft techniques. The combination of widespread browser adoption and relatively limited detection coverage creates opportunities for attackers to access stored credentials across enterprise environments.
Effective defense requires understanding the technical mechanics of browser credential storage, implementing comprehensive monitoring across multiple data sources, and developing correlation capabilities that identify suspicious patterns. Organizations must balance detection coverage with operational overhead, particularly regarding DPAPI event volume.
The shift toward browser-based credential attacks underscores the importance of defense-in-depth strategies that extend beyond traditional memory-based protection mechanisms. As browsers continue serving as credential repositories, security teams must adapt detection strategies to address this attack vector effectively.