Threat Attribution: Why Structure Beats Speculation And How Hawkeye Delivers Both

When a breach occurs, most security teams move fast on containment. Systems get isolated, backups get activated, and logs get pulled. But there is a question that too often comes last, if it comes at all: Who did this, and what are they after?
That question is the domain of threat attribution, the structured process of linking cyberattacks to specific individuals, groups, or nation-state actors. When attribution is done well, it transforms a reactive cleanup effort into a strategic intelligence advantage. It tells security leaders not just what happened, but what to expect next.
Without a structured approach to attribution, security teams operate on assumptions, intuition, or borrowed labels from other vendors. None of those hold up under scrutiny, and all three can lead to decisions that misalign defenses, misallocate resources, or worse, trigger the wrong response entirely.
What Threat Attribution Actually Means
Threat attribution is the practice of identifying who is behind a cyberattack, and, critically, why and how. It encompasses technical analysis, behavioral profiling, and contextual intelligence gathered across multiple data points over time.
Done well, attribution connects an intrusion to an adversary by examining consistent patterns: the tools they build, the infrastructure they favor, the victims they select, and the tradecraft they repeat. Done poorly, it produces labels that create a false sense of certainty and push defenders in the wrong direction.
The challenge is that attribution is structurally difficult. Threat actors reuse infrastructure, share toolkits, and intentionally blur their tracks. A single indicator of compromise (IoC), an IP address, a domain, or even a piece of malware rarely tells the full story. Multiple indicators might still not be enough without a structured way to weigh and correlate them.
How Structured Attribution Actually Works
Rigorous attribution builds from four interconnected analytical nodes: adversary, capability, infrastructure, and victim, the core components of the Diamond Model of Intrusion Analysis. The model forces evidence to be evaluated across multiple dimensions simultaneously, rather than anchored to a single artifact like an IP address or a file hash.
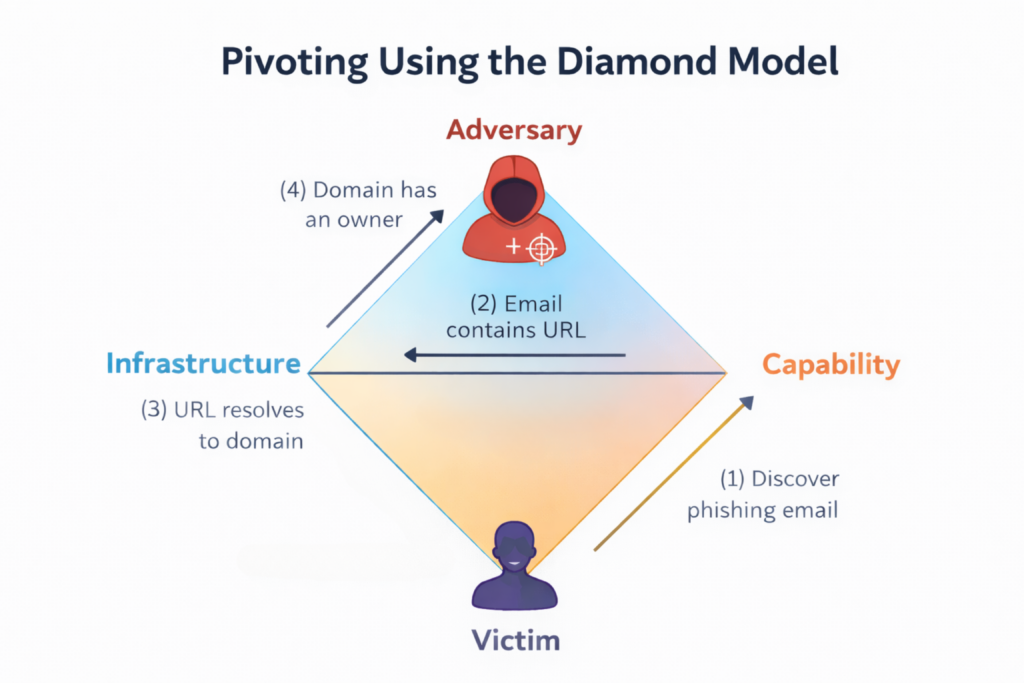
The Diamond Model maps every intrusion across four nodes. When evidence converges across all four, not just one, attribution confidence becomes defensible.
A single IP address carries very limited attribution weight. IP addresses are dynamic, shared, and easily spoofed. Custom malware reflects deliberate development investment and often persists across campaigns. Consistent targeting of a specific sector over time reflects strategic intent. When those signals converge, corroborated by multiple independent sources, a credible attribution picture forms.
Evidence quality is graded using the Admiralty System, an intelligence-community standard that scores source reliability (A through F) and information credibility (1 through 6) independently. This prevents analysts from treating all evidence equally, which is where bias and noise tend to enter the process. Layered on top of that, behavioral profiling against MITRE ATT&CK maps observed techniques to known adversary patterns, giving analysts a repeatable method for evaluating what the evidence actually supports, and what it does not.
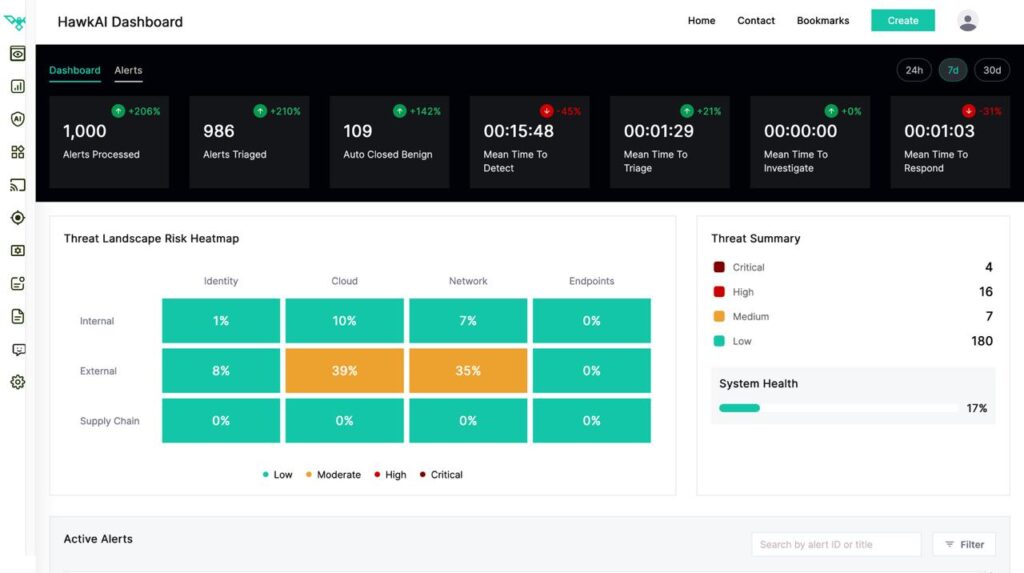
Hawkeye’s intelligence workflows are built around this principle. Hawkeye AI platform formalizes how evidence gets scored, how alternative explanations get tested, and how activity clusters move from provisional tracking to confirmed actor designations.
The Diamond Model: A Structured Starting Point
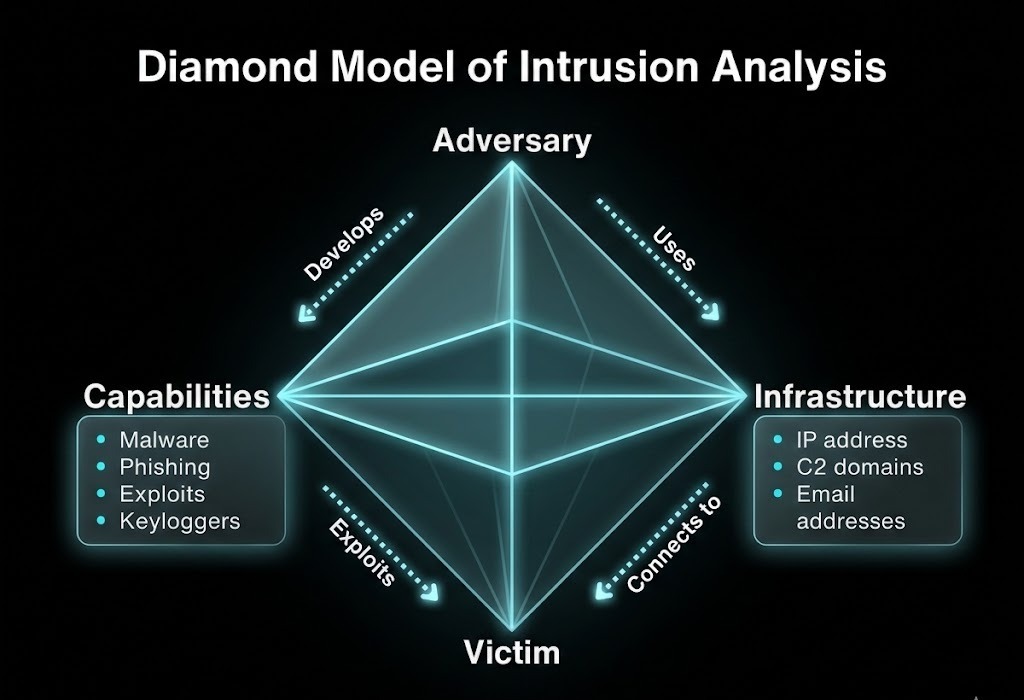
The Diamond Model of Intrusion Analysis is the most widely adopted foundation for disciplined attribution. It organizes intrusion activity into four interconnected nodes: adversary, capability, infrastructure, and victim. Rather than fixating on a single artifact, analysts examine how these nodes relate across multiple incidents.
The power of this model is relational. When the same tooling, the same targeting logic, and the same infrastructure patterns appear across separate attacks, confidence in attribution starts to build. One node in isolation proves little. Evidence aligning across all four nodes, that’s where defensible attribution begins.
This is the principle that drives how Hawkeye approaches intelligence, formalizing how evidence gets scored, how alternative explanations get tested, and how activity clusters move from provisional tracking to confirmed actor designations. The discipline is baked in: an actor doesn’t get named until the data actually supports it.
Why Attribution Matters Beyond Incident Response
Security leaders often treat attribution as an IR-specific concern, something that matters only after an attack is contained. But attribution intelligence shapes decisions well before and after any single incident.
Risk prioritization. Knowing which threat actors target your sector, what their capabilities look like, and what motivates them, espionage, financial gain, or sabotage, changes how you rank vulnerabilities and allocate defensive effort. A financially motivated group and a nation-state espionage actor require fundamentally different responses, even if they use similar initial access techniques.
Defensive posture. Actor-linked TTPs inform detection engineering. If you know an adversary consistently uses a specific persistence mechanism or favors particular command-and-control protocols, you can build detections tuned to those behaviors rather than waiting for known signatures.
Board-level communication. Regulators, boards, and insurance carriers increasingly ask security leaders to explain not just what happened, but who and why. Attribution evidence that is structured and scored provides defensible answers, rather than guesswork dressed up as confidence.
The Problem With Premature Labeling
One of the most persistent risks in threat intelligence is rushing to name an actor. The incentive to publish fast, to attach a memorable name, and link activity to a known group, can push analysts to skip the verification steps that make attribution credible.
This produces cascading problems. Misattribution causes organizations to build defenses against the wrong actor. It skews threat modeling. It can trigger operational, legal, or executive responses based on flawed conclusions. And when the mistake surfaces, it undermines trust in the entire intelligence program.
Rigorous frameworks address this by separating provisional tracking from formal attribution. Activity that shares patterns gets clustered and monitored under a temporary label. That cluster only gets elevated to a named intrusion set when evidence across multiple analytical dimensions meets a defined confidence threshold, reviewed and stress-tested, not declared by a single analyst under time pressure.
How Hawkeye Brings This Structure to Your Security Operations
For security teams without a dedicated threat intelligence unit running structured attribution workflows, this level of rigor can feel out of reach. That’s exactly the gap that Hawkeye is built to close.
Hawkeye’s CSOC and XDR capabilities are purpose-built for teams that need structured, evidence-grounded intelligence integrated directly into their detection and response workflows, not delivered as a separate report that arrives after decisions have already been made. Attribution context is operationalized: analyst teams work with actor-linked TTPs, behavioral patterns, and confidence-weighted intelligence that surfaces at the moment it’s needed.
Where attribution gets particularly complex, in multi-stage attacks, persistent adversaries, or incidents involving shared tooling, Hawkeye’s adversarial SecOps model provides the framework for thinking like the attacker. Mapping adversary behavior, sequencing likely next moves, and stress-testing defensive assumptions against real actor tradecraft gives security leaders the situational clarity that generic threat feeds simply can’t provide.
Hawkeye’s integration ecosystem means this intelligence doesn’t live in isolation. It flows into the tools your team already uses, enriching alerts, informing triage decisions, and giving analysts the attribution context they need to move from detection to a calibrated response, without losing time to manual correlation.
Conclusion: The Cost of Getting Attribution Wrong
Every attribution decision carries weight. Get it right, and your team responds to the correct threat, with the right controls, communicated to the right stakeholders. Get it wrong, and you spend resources defending against an actor who was never in your environment while the real one remains undetected.
The difference between those two outcomes is rarely a matter of tools or budget. It comes down to whether attribution is treated as a structured discipline or an educated guess dressed up as intelligence. Structured attribution demands evidence weighting, behavioral correlation, bias testing, and a willingness to sit with uncertainty rather than force a premature conclusion.
Security leaders who embed this discipline into their operations, through platforms built to operationalize intelligence rather than simply surface it, are the ones making decisions grounded in what can be proven, not what sounds plausible. In a threat environment where adversaries are deliberate, patient, and methodical, defenders cannot afford to be anything less.