HawkEye SOAR
SOAR (Security Orchestration, Automation, and Response) is a category of security solutions that combine three core functions — orchestration, automation, and response — into a unified platform. SOAR platforms are designed to improve the efficiency and effectiveness of Security Operations Centers (SOCs) by automating routine security tasks, orchestrating complex workflows, and enabling faster, more consistent incident response.
Orchestration
Automation
Response
SOAR facilitates faster and more accurate incident response by providing predefined playbooks and workflows that guide analysts through the response process. This ensures that incidents are handled consistently and in accordance with best practices, reducing the likelihood of errors and improving overall response times.
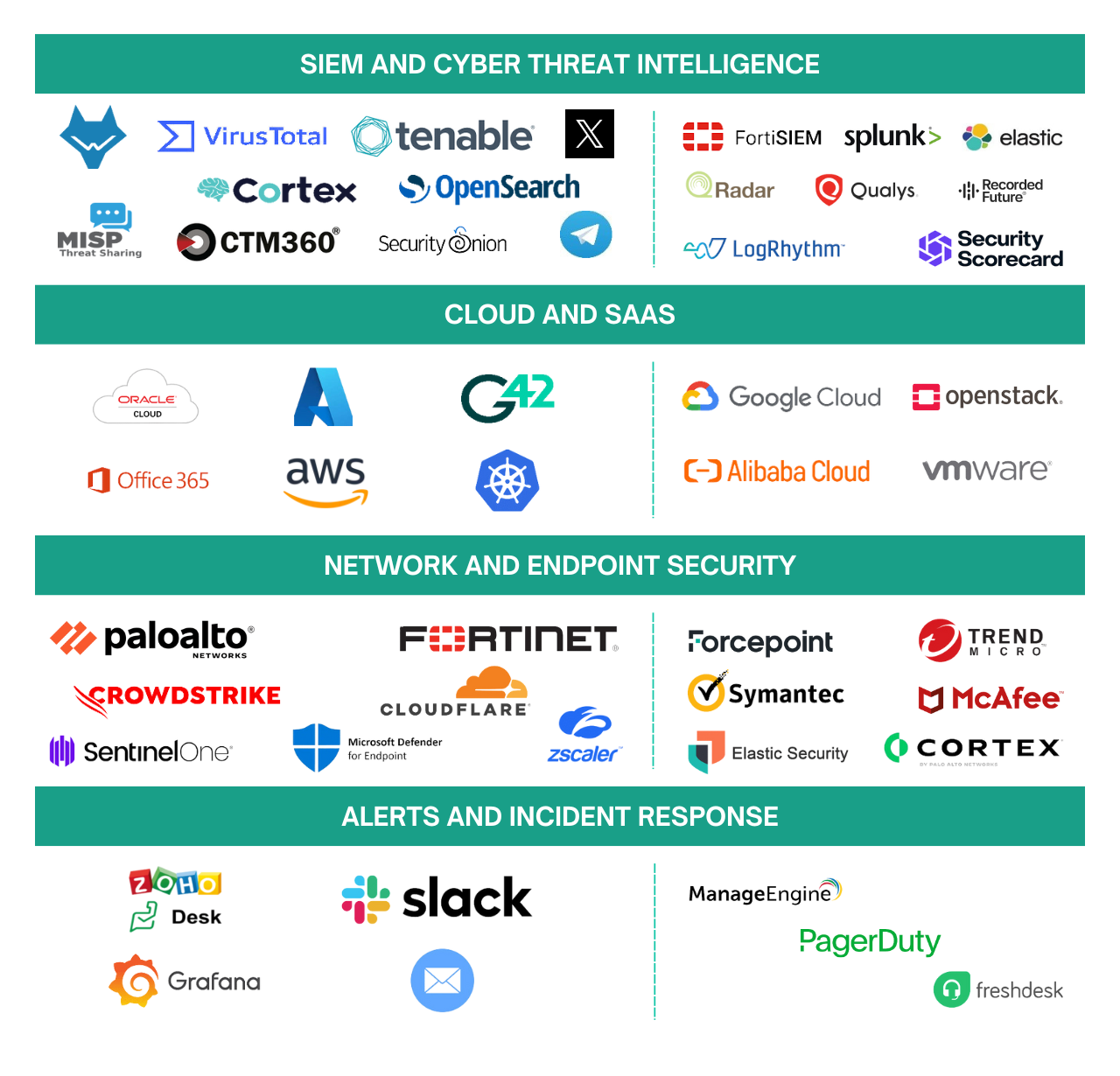
Integration Capabilities and Supported Platforms
SOAR Use Cases
HawkEye SOAR use cases are divided into categories as seen below.
01. Collect
Aggregating and centralizing data from various sources to ensure comprehensive visibility and real-time analysis in the SOC.
02. Enrich
Enhancing raw data with contextual information, such as threat intelligence and geolocation, to improve the accuracy of threat detection and investigation.
03. Detect
Identifying potential security incidents through advanced analytics, machine learning, and correlation of enriched data against known threat patterns.
04. Respond
Automating and orchestrating actions to contain, mitigate, and remediate security incidents swiftly and effectively.
05. Verify
Continuously validating the effectiveness of security measures, monitoring the threat landscape, and ensuring the integrity of response actions.
Sample Use Cases
Below are a few sample use cases for each of the categories.
01. Collect
Our collection capabilities are designed to seamlessly integrate various data sources into our SIEM, enabling comprehensive monitoring and analysis.
- EDR to SIEM
- Cloud to SIEM (API)
- Cloud to SIEM (Webnook)
02. Enrich
We enhance our collected data with additional context, allowing for more informed decision-making and improved threat detection.
- Enrichment of SIEM events with Cyber Threat Intelligence
- Enrichment of SIEM events with Geo-IP data
03. Detect
Our detection capabilities employ advanced algorithms and machine learning to identify threats across our monitored environments.
- SIEM Logs to ML Framework
- Scheduled SIEM aggregated searches
04. Respond
We automate responses to detected threats, ensuring rapid containment and mitigation of risks.
- Trigger Scans on EDR
- Quarantine Hosts
- Block IOCs on Firewall
05. Verify
Verification processes are in place to ensure the continuous effectiveness of our security measures.
- Discover Vulnerabilities
- Web service health checks
- Monitoring threat landscape
- Monitoring for impersonating domains
- Automated email reports